Expressvpn Glossary
Data governance framework
What is a data governance framework?
A data governance framework is a set of policies, roles, and processes that guide how an organization manages its data. It defines who owns specific datasets, how they are classified, and the rules that guide their accuracy, security, and use.
How does a data governance framework work?
A data governance framework works by assigning responsibility for how each important dataset is handled. A designated data owner (the person responsible for a data set) defines how the dataset is used and who can access it. Data stewards maintain the dataset’s definitions and structure so that it stays consistent across the organization. Meanwhile, technical teams configure the systems that store and process the data to support these rules.
Key components of a data governance framework
A data governance framework includes several core elements that support consistent and controlled data management.
- Policies and standards: These documents specify how data should be collected, labeled, stored, shared, and deleted.
- Data stewardship: Stewards oversee important datasets and ensure their structure and definitions stay consistent across systems.
- Access control: This defines which groups or roles can view, change, or delete different types of data.
- Data catalogs: Catalogs list key datasets along with their owners, sensitivity levels, and update schedules.
- Security and compliance tools: Encryption, logging, monitoring, and other controls enforce rules and demonstrate compliance with internal and regulatory requirements.
Why is a data governance framework important?
A data governance framework is important because it helps organizations: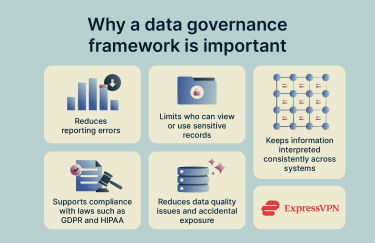
- Trust their data: Clear rules and consistent definitions prevent reporting errors and conflicting metrics.
- Protect sensitive information: Access controls limit who can view or use confidential data.
- Meet regulatory requirements: Documented handling and retention processes support compliance with laws like the General Data Protection Regulation (GDPR) and the Health Insurance Portability and Accountability Act (HIPAA).
- Reduce operational risk: Standardized practices lower the chance of data quality issues or accidental exposure.
- Keep data consistent across systems: Shared definitions ensure teams use the same meaning and version of information.
Security and privacy considerations
Protecting sensitive information is a key part of any data governance framework. Organizations typically use encryption to safeguard data both at rest and in transit and apply role-based access controls (RBAC) so only the right people can view or change specific datasets. Regular audits, monitoring activities, and data lineage reviews help confirm that data is being handled according to policies and regulatory requirements.
In hybrid or remote environments, organizations use enterprise virtual private networks (VPNs) or zero-trust access solutions to authenticate users, enforce device requirements, and ensure connections follow governance policies. When employees work from public or less-secure networks, a personal VPN can add an extra layer of encryption at the individual level.
Common data governance framework models
Organizations choose a governance model based on their size, structure, and how broadly data is used. The main models are:
- Centralized governance: One team sets policies, approves changes, and manages key data standards.
- Decentralized governance: Individual departments manage their own datasets within high-level organizational guidelines.
- Hybrid (federated) governance: Central teams maintain core policies, shared standards, and security expectations, while departments handle day-to-day decisions for the data they own.
Common challenges
Organizations often face several obstacles when establishing data governance, including:
- Unclear data ownership: Difficulty deciding who is responsible for specific datasets.
- Inconsistent data definitions: Different teams using their own terminology or rules.
- Poor data quality: Duplicate, outdated, or incomplete information.
- Limited adoption: Resistance to new processes or unclear expectations.
- Complex regulations: Evolving privacy and compliance requirements.
- Legacy systems and silos: Older tools or isolated data sources that are hard to integrate.
Further reading
- Zero-trust cloud security explained
- What is the Internet of Behaviors (IoB)?
- How does the internet work?
