Expressvpn Glossary
Secure coding
What is secure coding?
Secure coding is the practice of writing software in ways that reduce security vulnerabilities. Rather than addressing security issues after release, protections are built into the development process from the start, guided by secure coding standards.
Most developers follow established frameworks such as the Open Web Application Security Project (OWASP). These guidelines emphasize practices such as validating external data, restricting system permissions, and protecting sensitive data.
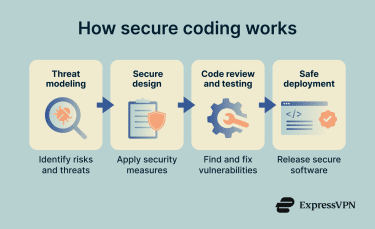
How does secure coding work?
Secure coding integrates security practices throughout the development process, before deployment.
Common practices include:
- Threat modeling before coding: Development teams analyze how a system or feature could be abused to identify sensitive data flows and potential attack points.
- Safe defaults and least privilege: Applications and services receive only the permissions required to perform their tasks, reducing the potential impact of compromise.
- Input validation and encoding: Applications validate and sanitize external data and properly encode output to prevent attacks such as cross-site scripting (XSS).
- Secure error handling: Error messages avoid exposing internal system details; technical information is logged internally instead.
- Code review and testing: Peer review and automated tools, including static application security testing (SAST), which analyzes code without executing it, and dynamic application security testing (DAST), which tests running applications, help detect vulnerabilities before release.
Types of secure coding practices
Developers use several practices to strengthen application security and protect sensitive data.
- Input validation and output encoding: Applications verify incoming data and encode output before displaying it, helping prevent attacks such as Structured Query Language (SQL) injection and XSS.
- Authentication and session management: Secure authentication methods confirm and protect user identities, while session controls help prevent unauthorized access or session hijacking.
- Authorization and access control: Authorization controls define what authenticated users can do, enforcing least-privilege access to limit unauthorized actions.
- Cryptography and secret management: Sensitive data is protected using established encryption methods, while secrets such as API keys or passwords are stored securely rather than in source code.
- Secure logging and monitoring: Applications record security-relevant events while avoiding storing sensitive information such as plaintext credentials.
Why is secure coding important?
Many cyberattacks exploit weaknesses in software. Vulnerabilities in input handling, authentication systems, or data protection mechanisms can allow attackers to access sensitive information and disrupt systems.
Addressing security during development reduces the likelihood of breaches and is more cost-effective than fixing vulnerabilities after release.
Common vulnerabilities secure coding helps prevent
Secure coding practices are designed to prevent common software vulnerabilities, including:
- SQL injection: Attackers manipulate database queries through malicious input.
- XSS: Malicious scripts are injected into a webpage and executed in a user’s browser.
- Buffer overflow: A program writes more data to a memory buffer than it can hold, potentially allowing arbitrary code execution.
- Broken authentication: Weak authentication or session controls allow attackers to bypass login controls.
- Insecure deserialization: Manipulated serialized data triggers unintended behavior or unauthorized code execution.
Further reading
- Why software security audits matter
- Privacy engineering: Principles, benefits, and best practices
- Security concerns in cloud computing and how to address them
- What is a buffer overflow, and why is it dangerous?
- Supply chain attack: How it works and how to stay protected

